Envision a world where your refrigerator not only keeps your food cold but also alerts you when groceries are running low, where your car schedules its maintenance appointments, and where factories run smoothly without human intervention. It is not science fiction—it’s the reality of devices communicating with each other. In this interconnected world, machines talk to each other, sharing data and making decisions autonomously. By leveraging the power of wireless sensors, the Internet, and advanced computing, machine to machine (M2M) communication is transforming industries. Let’s dive into what M2M communication is, its key features, and the applications driving the future of technology.
What is Machine to Machine (M2M) communication?
Machine to machine (M2M) communication means the automated exchange of information between devices without human intervention. This technology allows machines, sensors, and other devices to communicate directly, enabling real-time data sharing and operational efficiency. M2M is a foundation for the Internet of Things (IoT), powering various applications from industrial automation to smart homes.
How M2M Works?
M2M communication works through a series of steps that ensure data is collected, transmitted, processed, and acted upon efficiently:
- Data Collection: Sensors or devices gather data from their environment. It could include temperature readings, equipment status, or location information.
- Transmission: The collected data is sent to a central system. It can occur via various communication networks such as cellular, Wi-Fi, satellite, or wired connections.
- Processing: The central system, often a server or cloud-based platform, processes the received data. It involves analyzing, storing, and making decisions based on the data.
- Action: Automated actions are initiated based on the processed data. For instance, if a machine detects an anomaly, it might send an alert, or a system automatically adjusts to optimize performance.
Key Features of Machine to Machine (M2M)
M2M communication boasts several defining features:
- Automation: Reduces the need for human intervention, increasing efficiency and reducing the potential for human error.
- Scalability: Can be deployed across vast networks of devices, from a single factory to global logistics systems, handling thousands or even millions of connections.
- Real-Time Monitoring: Provides immediate insights and actions based on live data, allowing quick responses to changing conditions.
- Interoperability: Supports various devices and communication protocols, ensuring compatibility and seamless integration with existing systems.
- Remote Management: Enables remote monitoring and control devices from any location, facilitating maintenance and troubleshooting without physical presence.
- Data-Driven Decision Making: Uses collected data to inform decisions and optimize operations. It leads to improved performance and efficiency.
- Cost Efficiency: Reduces operational costs by automating processes, improving resource management, and minimizing downtime through predictive maintenance.
- Enhanced Security: Incorporates advanced security measures to protect data integrity and prevent unauthorized access.
Applications and Examples of M2M Communication:
Here are some of the key ways M2M communication is used in various sectors:
- Smart Metering:
- Utility companies remotely monitor energy consumption using M2M, with smart meters collecting data for billing and analysis.
- Fleet Management:
- GPS tracking devices in vehicles communicate location and performance data, enabling real-time monitoring and route optimization.
- Healthcare Monitoring:
- Wearable fitness trackers transmit health metrics to healthcare providers for remote monitoring and intervention.
- Industrial Automation:
- Example: Sensors in machinery collect performance data, enabling predictive maintenance and optimizing production efficiency.
- Smart Agriculture:
- Soil sensors and drones collect crop data, allowing farmers to make informed decisions on irrigation and pest control.
M2M vs. IoT
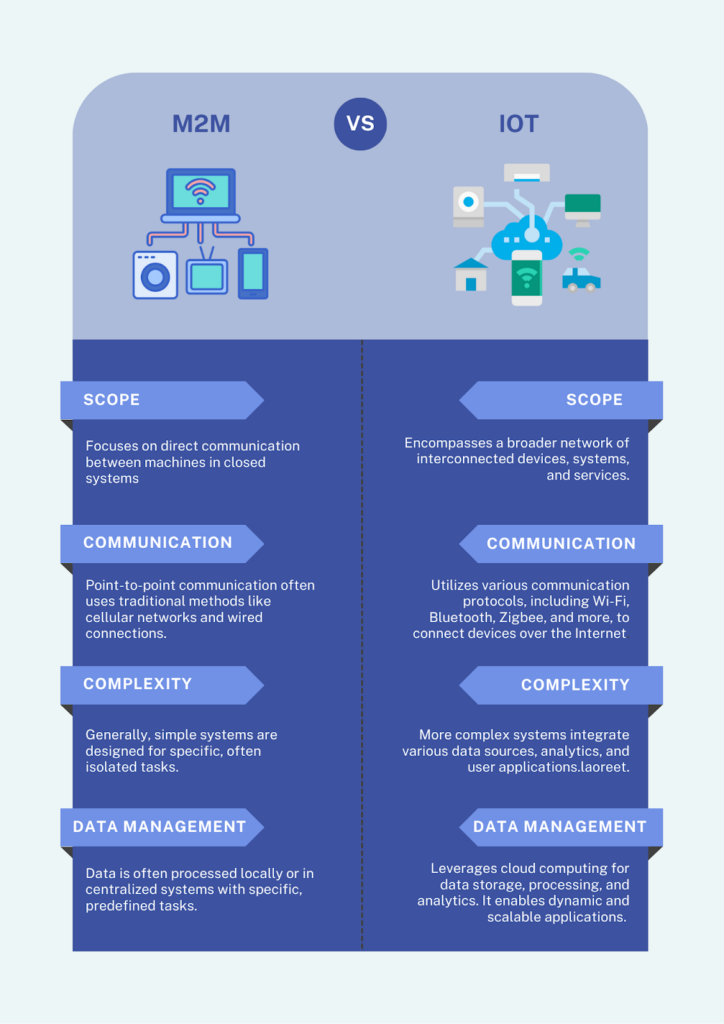
The image below highlights the key differences between M2M and IoT:
M2M Communication and Security
Security is a critical aspect of M2M communication, as interconnected devices are susceptible to a wide range of cyber threats, including data breaches, unauthorized access, and malware attacks. The proliferation of M2M devices in various sectors, from industrial automation to healthcare, has increased the attack surface, making robust security measures essential. Ensuring data integrity, confidentiality, and availability is crucial to maintaining a secure M2M environment.
Machine to Machine (M2M) Security Best Practices
To safeguard M2M systems, consider these best practices:
1. Data Encryption:
Encrypt the data in transit and at rest to protect against unauthorized access and ensure data privacy.
2. Authentication and Authorization:
Implement a robust authentication mechanism to ensure that only authorized devices and users can access the network, preventing unauthorized access.
3. Regular Updates:
Keep firmware and software up-to-date to mitigate vulnerabilities and protect against emerging threats.
4. Network Segmentation:
Isolate M2M networks from other IT infrastructure to contain potential breaches and limit the spread of cyber attacks.
5. Monitoring and Auditing:
Continuously monitor network activity and conduct regular security audits to detect and respond to threats promptly, ensuring the system’s integrity and reliability.
Conclusion
Machine to machine (M2M) communication is not just a buzzword—it’s a reality reshaping industries and everyday life. As we’ve explored its applications and functionalities, one thing remains clear: the future is interconnected.
However, securing machine to machine systems is crucial to ensure data integrity and protect against cyber threats. Machine identity management is crucial for securing M2M systems. It involves authenticating machine credentials to ensure secure access to resources and communication within networks or online.
Consider exploring our comprehensive guide on non-human identities – challenges and solutions to understand more about M2M Identity Security. Schedule a demo today and discover how Entro Security can help protect your M2M systems.
FAQs
M2M (machine to machine) communication refers to the automated exchange of data between devices without human intervention. This technology enables machines, sensors, and systems to communicate directly with each other, allowing for real-time data collection, processing, and actions in applications such as industrial automation, smart metering, and fleet management.
M2M vs. IoT
M2M involves direct communication between devices for specific tasks within closed systems, using traditional communication methods. IoT connects a broader network of devices, including user interfaces and cloud applications, across various communication protocols. M2M is common in industrial settings, while IoT spans consumer and commercial applications like smart homes and wearable devices.